Introduction
A user logs into your application successfully—but gains access to data they shouldn’t see.
This is not a login problem.
It is a system design problem.
In modern web applications, security is no longer limited to protecting login forms. It extends across APIs, microservices, third-party integrations, and distributed systems. As applications scale, managing who a user is (authentication) and what they can do (authorization) becomes increasingly complex.
When these two are not properly designed, the result is not just a bug—it’s a security risk with real business impact.
Concept Foundation
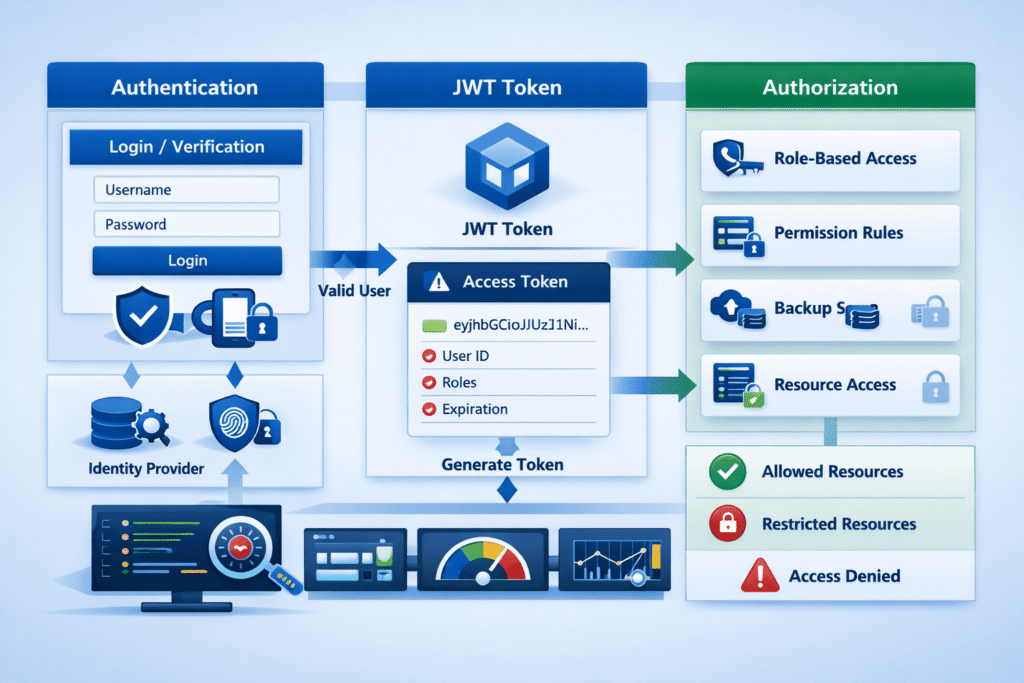
Authentication and authorization are often used interchangeably, but they solve different problems:
- Authentication → Verifies identity (Who are you?)
- Authorization → Defines permissions (What can you access?)
A typical flow looks like:
- User provides credentials (login)
- System verifies identity (authentication)
- System assigns permissions (authorization)
- User interacts with the system based on allowed actions
Modern systems implement this using:
- Tokens (JWT, OAuth)
- Role-based or attribute-based access control
- API-level security mechanisms
The key principle:
Authentication proves identity. Authorization enforces boundaries.
How the Problem Occurs
Security issues often arise not from missing authentication, but from weak or poorly structured authorization logic.
Common causes include:
- Hardcoded permission checks scattered across code
- Overly broad access roles (e.g., “admin” everywhere)
- Missing validation at API endpoints
- Trusting frontend logic for access control
These issues lead to:
- Unauthorized data access
- Privilege escalation
- Inconsistent permission enforcement
The system appears secure—but has hidden vulnerabilities.
1. Authentication Mechanisms: Beyond Username and Password
Traditional authentication relied on:
- Username + password
Modern systems require stronger approaches:
- Token-based authentication (JWT)
- OAuth / Social login (Google, GitHub, etc.)
- Multi-Factor Authentication (MFA)
Why this matters:
- Stateless authentication improves scalability
- Tokens allow secure communication across services
- MFA reduces risk of credential compromise
Key consideration:
Authentication should be secure, scalable, and user-friendly.
2. Token-Based Authentication and JWT
JSON Web Tokens (JWT) are widely used in modern applications.
A JWT typically contains:
- User identity
- Expiration time
- Claims (roles, permissions)
Flow:
- User logs in
- Server issues a token
- Client sends token with each request
- Server validates token
Benefits:
- Stateless (no server-side session storage)
- Works well with APIs and microservices
- Scales easily across distributed systems
Risk:
If not handled properly:
- Token leakage = full access
- Long-lived tokens increase vulnerability
3. Authorization Models: RBAC vs ABAC
Authorization defines what users can do.
Role-Based Access Control (RBAC)
- Users are assigned roles (Admin, Editor, User)
- Permissions are tied to roles
Pros:
- Simple to implement
- Easy to manage for small systems
Cons:
- Becomes rigid as system grows
- Role explosion (too many roles)
Attribute-Based Access Control (ABAC)
- Access is based on attributes:
- User attributes (role, department)
- Resource attributes
- Context (time, location)
Pros:
- Highly flexible
- Scales with complex systems
Cons:
- More complex to implement
Key insight:
RBAC works for simple systems.
ABAC is better for scalable, dynamic applications.
4. Securing APIs: The Real Enforcement Layer
In modern applications, the backend API is the true gatekeeper.
Even if the frontend hides features, users can still:
- Inspect API calls
- Modify requests
- Attempt unauthorized access
Best practice:
Always enforce authorization at the API level.
Common mistakes:
- Trusting frontend validation
- Missing permission checks in endpoints
- Exposing sensitive data through APIs
Solution:
Every API request must:
- Verify authentication (token validation)
- Check authorization (permission validation)
5. Session vs Token-Based Authentication
Two common approaches:
Session-Based Authentication
- Server stores session data
- Client uses cookies
Pros:
- Simpler for traditional apps
- Easy to invalidate sessions
Cons:
- Harder to scale
- Requires server-side storage
Token-Based Authentication
- Client stores token
- Server validates token per request
Pros:
- Stateless and scalable
- Ideal for APIs and microservices
Cons:
- Token management complexity
- Harder to revoke instantly
6. Handling Permissions in Distributed Systems
Modern systems often include:
- Microservices
- Third-party APIs
- Multiple backend services
This introduces challenges:
- Consistent permission enforcement
- Token validation across services
- Secure service-to-service communication
Solutions:
- Centralized authentication service
- API gateways for validation
- Shared identity providers
Key principle:
Security should be centralized but enforceable everywhere.
7. Common Security Risks and Vulnerabilities
Poor authentication and authorization lead to:
- Broken Access Control – Users access restricted data
- Token Hijacking – Stolen tokens used for unauthorized access
- Privilege Escalation – Users gain higher access than intended
- Insecure Direct Object References (IDOR) – Accessing resources via manipulated IDs
Example:
A user changes an ID in a URL and accesses another user’s data.
Prevention:
- Always validate permissions
- Never trust user input
- Use secure token handling
8. Logging, Monitoring, and Auditing
Security is not just prevention—it is visibility.
A maintainable system includes:
- Access logs
- Authentication attempts
- Permission checks
Why this matters:
- Detect suspicious activity
- Trace security incidents
- Improve system reliability
Best practice:
Log meaningful events—not just errors.
Practical Implementation
To implement secure authentication and authorization:
Step 1: Choose Authentication Strategy
- JWT or session-based depending on system
- Add MFA for sensitive applications
Step 2: Define Authorization Model
- Start with RBAC
- Move to ABAC if needed
Step 3: Secure APIs
- Validate tokens on every request
- Enforce permission checks
Step 4: Centralize Security Logic
- Avoid scattered checks
- Use middleware or guards
Step 5: Implement Monitoring
- Log access attempts
- Track anomalies
Step 6: Regular Security Audits
- Test for vulnerabilities
- Update dependencies
Common Mistakes
1. Confusing authentication with authorization
Login success does not mean access is valid.
Better approach: Separate identity and permission logic.
2. Trusting frontend controls
Hidden buttons do not equal security.
Better approach: Enforce rules in backend APIs.
3. Overusing admin roles
Broad access increases risk.
Better approach: Use granular permissions.
4. Ignoring token security
Improper storage leads to token theft.
Better approach: Use secure storage and expiration.
Key Takeaways
- Authentication verifies identity; authorization controls access
- Token-based systems are essential for modern scalable apps
- API-level security is critical for real protection
- RBAC works for simple systems; ABAC for complex ones
- Security must be centralized but enforced consistently
- Logging and monitoring are key to long-term security
Conclusion
Authentication and authorization are not just features—they are foundations of system design.
As applications grow, the complexity of managing identity and access increases. Without a structured approach, systems become vulnerable—not because of obvious flaws, but because of inconsistent enforcement.
A secure system is not defined by how users log in.
It is defined by how well the system controls what happens after login.
In modern web applications, security is not optional—it is architectural.